Imagine you’re running your dream business, and you’ve been able to scale it to make massive profits. You have a team of loyal employees and an excellent office space.
But you aren’t a technology expert, and you aren’t sure if your company is at risk of a cyberattack. You can review your risk with a risk assessment that follows the NIST 800-30 framework.
Keep reading for some tips on how to run the assessment and use the results to help your company.
Include the Entire Organization
The first tip for your next NIST 800-30 risk assessment is to include every part of your company. You can’t run a risk assessment for every department at once, but you should run individual assessments within each area that uses IT systems.
That way, you won’t have to worry about missing any security issues. You may find something in a department that you didn’t expect. Perhaps your accounting team has a security problem.
If you only run a NIST SP 800-30 on a few teams, you could miss something major. So don’t be afraid to run more risk assessments, even if it seems like overkill.
“The assessment should be thorough, so don’t try to rush through it. Give yourself enough time to prepare for the assessment, run it, and review the results after the fact. “
Give Yourself Time
Because you should run a NIST SP 800-30 risk assessment for your entire business, you may need time for the test. You don’t have to test each area at the same time, and it can take a few days to cover each department.
The assessment should be thorough, so don’t try to rush through it. Give yourself enough time to prepare for the assessment, run it, and review the results after the fact.
That way, you can make sure you get an accurate NIST 800-30 summary that you can use to improve your business.
Keep an Open Mind
If this is your first time running a risk assessment based on NIST 800-30, you probably don’t know what to expect from the results. But even if you’ve used the framework before, you can’t know what the assessment will show.
You should go into any risk assessment with an open mind. Of course, you don’t want to think about any potential issues with your company.
However, you may have some vulnerabilities or threats to consider. Being open-minded can help you learn from this risk assessment and better your organization.
Be Flexible
Once you set your initial assessment process with NIST SP 800-30, it can be easy to set it and forget it. But like other areas of IT, risk assessment needs to change over time.
New software versions come out, and overall IT systems experience changes. Hackers can develop new security threats and find unique vulnerabilities.
Because of that, you should adjust your risk assessment process. You should stay up-to-date with cybersecurity regulations so that you can follow the best procedure before your next risk assessment.
Determine the Assessment Purpose
Consider your goals for running a NIST 800-30 assessment. Of course, you want to discover any vulnerabilities in your IT infrastructure.
But you can go deeper than that with the purpose. Perhaps you want to increase profits for your business, or you want to train your IT staff on new technological challenges.
If you have a specific goal, that can help you determine where to start your assessment. That way, you know which departments to focus on first and how you want to move throughout the company.
Figure Out What the Assessment Covers
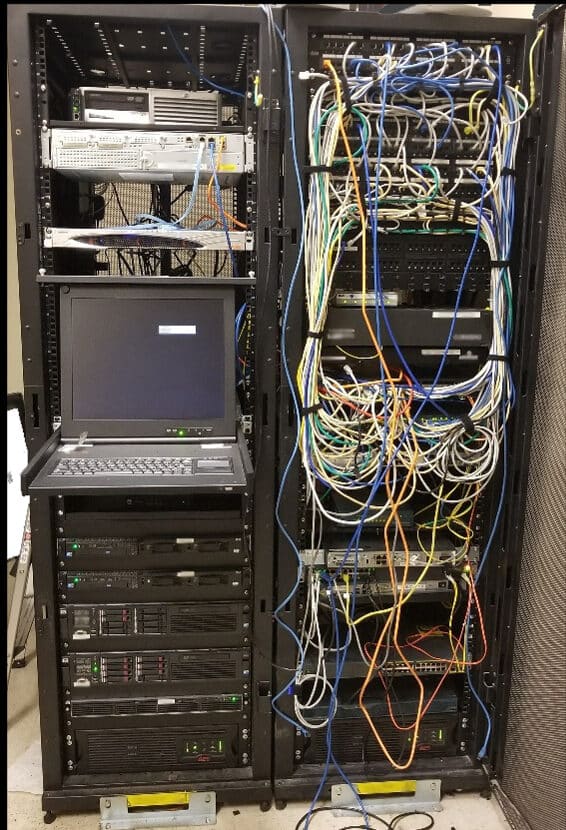
You should also determine the assessment scope. Your risk assessment should include software and hardware that you use in your business.
It should also cover data and determine critical data for your organization. As mentioned, your assessment should cover all areas of your business.
Knowing the risk assessment scope can help you prepare to follow NIST 800-30 standards. That can help the assessment go more smoothly. While you may encounter vulnerabilities, you can ensure you can check for all security problems.
Consider Assessment Assumptions and Constraints
A NIST SP 800-30 risk assessment does have some constraints that you need to think about. While you can review your entire organization and check for various vulnerabilities, you do have to follow the right standards.
The assumption is that you will conduct the assessment with 800-30 standards in mind. If you don’t for some reason, you may not be able to interpret the results in the same way.
Consider how such assumptions and constraints can affect your risk assessment results and what you do with the information. Then, you can make sure you can improve your cybersecurity after each assessment.
Run a Risk Assessment
Now, you’re ready to run your next risk assessment with NIST SP 800-30. You should follow a few steps to make the most of the assessment.
Whether your company uses Windows or Mac computers, you can use the same process. Here’s how you can run your next risk assessment.
Identify Threats
First, you need to check various systems and characterize them. Software and system interfaces help characterize systems and hardware that you use in your business.
Your assessment should also identify data on your company system and which employees can access the data. Then, you also have to define the system functions, boundaries, and objectives.
Finding critical data now will also help you gather information for potential threats. That way, you can use that data later in the assessment and after the results.
Check the Systems
Many companies deal with cybersecurity threats, and IT departments can help reduce the chance of those threats becoming attacks. Whether you use managed IT services or hire IT employees, they may not always catch threats.
When running a risk assessment, you can review your company’s history of cyberattacks. That can help you find current potential threats to include in the NIST 800-30 summary.
Find Vulnerabilities
Threats may not be a big deal to your company, but they can become a problem if your infrastructure has vulnerabilities. If there’s a spot in your system where hackers can get in, your system will have a higher risk score at the end.
You can use this step in the NIST 800-30 assessment to discover areas with a potential for exposure to threats. You’ll need to look over any previous risk assessments, run security tests, and map for vulnerabilities.
NIST 800-30 does this very well, and you can use the results to improve your security later.
Analyze Controls
Next, NIST 800-30 standards require that you analyze controls in your network. You should only do this step after you find vulnerabilities because the framework starts from the bottom.
Finding controls after you discover problems can help you mitigate those issues more quickly. You can use your controls to cover small security issues.
This step is essential if you have vulnerabilities, but it’s also useful if you don’t have problems. You can analyze your controls and make sure they work well in case of a future issue.
Review the Chances of an Attack
Once you analyze your controls, you can check sources of potential threats. You should review their motivation for attacking and their capacity to harm your systems.
The information will give you an overview of the chance of various threats attacking. If you have multiple potential threats, you should review the chances of each one.
That way, you can include as much information in your NIST 800-30 summary. You can then use that information to inform future cybersecurity updates and practices.
Consider Impact and Risk
At this point, you should have a good idea of the risk of cybersecurity issues facing your organization. You can measure the potential impact these risks have on your company, and you can determine how critical certain risks are.
Consider the controls and the probability of an attack, and you can then figure out the amount of risk you have. Then, you can use that data to make changes to your IT infrastructure.
Implement Recommendations
Once you know where you can improve your cybersecurity, you can implement recommendations from NIST 800-30 standards. The recommendations can focus on the possibility of threats and how you can reduce those chances.
You can also use the recommendations to mitigate the impact of an attack and reduce your overall risk.
The results should help your company, and you can use the data to make better decisions for your business. That way, you can keep your data safe while growing your business.
Share With Shareholders
If you have shareholders, you should share the NIST 800-30 risk assessment with your investors. While you should all agree to follow any recommendations, your stakeholders should have a say in what you do.
That way, you can keep your investors happy, and you can make sure they know what is happening in your business. Whether the results have you make small or big changes, everyone needs to be on the same page.
If you don’t have shareholders, you can consult with a business partner or high-ranking managers. That way, you can get feedback on potential changes, and you can verify that they will help all areas of your business.
Running Your Next NIST 800-30 Assessment
The NIST 800-30 framework has standards for how you can run a risk assessment. If you’re due for your next cybersecurity test, you can follow the framework and review the results.
But you should consider a few tips to make the most of the assessment. That way, you can use the results to grow your business.
Do you need help with cybersecurity testing? Learn more about our services and give us a call.
Contact us to learn more about how Bridgehead I.T. can help you align your I.T. with your business objectives.