As new cybersecurity laws emerge, it’s important to keep your services up-to-date. Dive into Cybersecurity Maturity Model Certification (CMMC) to stay on top.
In 2021, cyberattacks pose the fastest growing threat to America. This is also one of the hardest risks to understand. All businesses working with sensitive data need a Cybersecurity Maturity Model Certification (CMMC).
New laws related to CMMC compliance are now in effect. Keep reading to ensure that your business is meeting all the CMMC rules.
Understanding Cyber Security Maturity Models
CMMC is the Department of Defense’s (DOD) method for assessing a contractor’s security. The DoD released new CMMC standards in January 2020. All new DOD contracts must meet the CMMC Requirements by 2026.
Failure to follow these standards will make businesses ineligible to win contracts. The program’s rollout will start in 2021. Between 2021 and 2026 the government will only award contracts to compliant companies.
There are five CMMC levels. The specific contract agreement determines the required CMMC levels the company must meet.
Contractors may no longer self-report compliance. They must pass an audit from a certified third-party assessment organization (C3PAO).
Compliance Requirements for Cybersecurity in 2021
When creating and implementing a CMMC compliance plan, you must take several steps. Make sure each point of this CMMC compliance checklist is met.
NIST Special Publication 800-171, Revision 2Protect all Controlled Unclassified Information (CUI) kept in nonfederal systems and companies. CUI can directly impact the Federal Government’s mission completion and business operations.
Federal Security Requirements
Contractors must adhere to federal security requirements to protect confidential CUI. The company bears this responsibility in the following situations:
*When CUI is outside of federal systems and organizations
*When CUI-containing systems are used by non-federal workers on behalf of the contractor
*When there aren’t specified legal safeguard criteria for the CUI or its subcategories
Ensuring that your company adheres to these requirements helps your chances of winning contracts.
CMMC Readiness Assessment and Gap Analysis
Readiness assessments help discover non-compliant NIST 800-171 standard processes. This may include how you control access to and storage of data.
*Do you have an incident response plan in place?
*Is it current and effective?
*Have you fully trained all IT and other appropriate staff?
*How do you implement and maintain your established security protocols?
By answering these questions, you can create a gap analysis to identify problem areas.
Create a Remediation Plan
The next step is to create a remediation plan to correct these risk areas. You may use in-house resources or an outsourced managed security service provider (MSSP).Examples include:
*Action to resolve security issues
*Adjustment of resource allocation to mitigate issues and close security gaps
*A specific timeline for completing each task
*Description of how the security vulnerabilities were detected
*Quantification of priorities, risk levels, and approximate remediation cost
This should include an actionable and prioritized plan to address CMMC compliance gaps.
Plan for Continuous Cybersecurity Monitoring and Reporting
Following the remediation phase, you need a plan to maintain over-watch.
Since this can be a big job, many contractors choose to use an MSSP.
They’ll ensure continuous CMMC compliance monitoring. If they detect vulnerabilities, they’ll report them immediately. Then specialized experts use tools to correct the gap.
Build and Update Your System Security Plan (SSP)
After developing your SSP, it needs updating with all substantial security process changes. Include the following in your plan:
*Administrative tasks
*Company policies
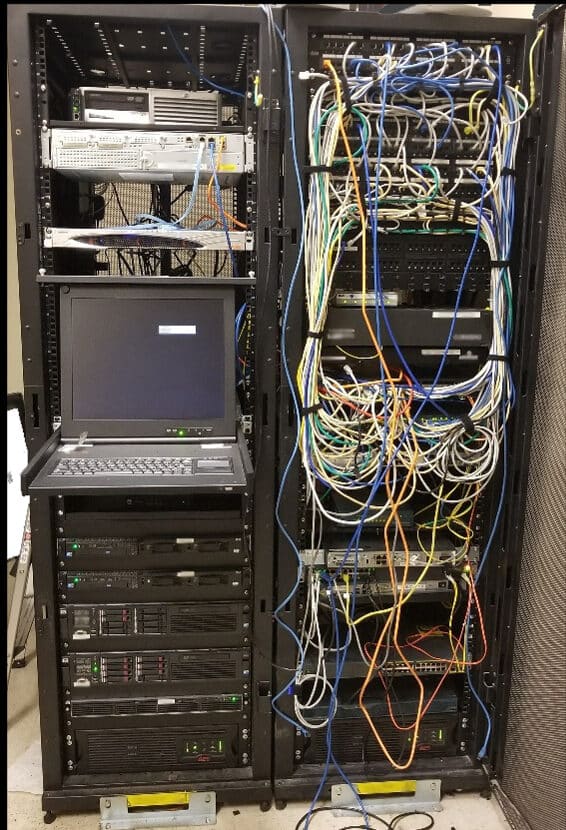
*Network diagrams
*Worker security responsibilities
*Description of CUI storage and transmission protocols
*Description of how data flows between systems
*Description of authorization and authentication processes
During the award contest, the DOD mandates a review of each contractor’s SSPs. It’s important to show documented reviews and updates to the SSP.
Cybersecurity Maturity Model Certification and FedRAMP Certification
U.S. federal agencies only work with certain cloud service providers (CSP). The government requires that the CSP be FedRAMP approved.
The Federal Risk and Management Program (FedRAMP) addresses cybersecurity risks. Federal companies may buy this program and use its cloud services and products.
To achieve FedRAMP compliance, the CSO must meet several requirements.
They must adhere to the following:
*Complete FedRAMP SSP documents
*Implement FIPS 199 category compliance controls
*Pass FedRAMP 3PAO assessment of cloud offerings
*Create a Plan of Action and Milestones
*Adhere to Joint Authorization Board (JAB) Provisional ATO (P-ATO) or Agency ATO
*Implement ongoing monitoring programs with monthly vulnerability scans
NIST 800-53 defines the FedRAMP requirements that the CPS must meet.
This provides a tool for meeting CMMC standards.
How Long Do Computers Last?
Part of CMMC compliance involves proper disposal of computers containing any CUI. Thus, including plans for hardware replacement is an important part of the plan.
In general, personal computers last about five to eight years. Laptops tend to have a shorter lifespan of around three to five years.
The Keys to Network Security and Monitoring
Endpoint security represents a key focus for preventing cybercrime. This involves making all endpoints that connect to any network secure. These endpoints are farthest away from the center.
Thus, it includes any IoT system or device that connects to the main network. Examples include mobile phones, user profiles, tablets, networks, and more.
Several endpoint security tools are often used to ensure the security of these IoTs.
Cloud solution track, and if needed, block endpoint access from a device or solution.
What is Microsoft Defender for Endpoint (MDE)?
MDE provides full control of your system’s security. It allows assessment of the network’s current state and watches for vulnerabilities. If it detects problems, it takes action to correct the weakness.
It uses various types of technology to protect enterprise business networks. MDE may work alone or in combination. Microsoft cloud services and Windows 10 OS have built MDE into their systems.
The MDE threat intelligence identifies the tools used by attackers. It’s also able to evaluate the techniques they are using.
It sounds an alert and collects sensor data to find key information. With this information, the MDE can generate countermeasures. This provides protection for your cloud.
MDE fights malware, spyware, and viruses to prevent device damage. It also protects sensitive data to prevent breaches.
When a problem is detected, MDE blocks or pauses processes. It then remediates advanced attacks on your endpoints. The MDE also investigates the scope and potential impact of the threat.
Keys to an Effective IT Automation Strategy
Many companies use artificial intelligence (AI), machine learning (ML), and DevOps workflows. This creates sophisticated, optimized, and efficient workflows. It is key for CIOs to explain what these processes can and can’t do.
Define the steps involved in existing processes. Differentiate between key steps and those that create bottlenecks.
Decide if problem areas need new requirements to meet growing needs.
Combining this knowledge with new technologies moves businesses toward automated strategies. Automation may be the solution to interruptions in workflow and increased security.
Edge Computing
Today it’s key for business leaders to understand the next era of computing. Edge computing decreases latency by shrinking the distance between IoTs and cloud-based processors. Download times are now up to 100 times faster with 5G than 4G.The Augmented Reality (AR) cloud is like a digital copy of the real world. Users can access it from any device. This uses technologies to create, position, and anchor digital content over physical objects.
Current technologies are fueling the evolution of the Spatial Web. The result will generate more advances on the horizon. This will increase the user’s interaction, information, and computational functions. AR and virtual reality (VR) devices will provide the main gateways to access the Spatial web. Devices may include AR glasses, IoT devices, digital contact lenses, autonomous vehicles, and more.
These AR interfaces need to be more affordable and comfortable. This will lead to wider adoption of these new technologies.AI and ML will play an integral role in Spatial Web computations. Machines and devices will gain the ability to understand non-digital work. Examples include natural language processing and computer vision.
Advances will allow computers to comprehend context and personalize experiences. They’ll also have the ability to make contextual decisions and continuously learn.
Increased availability of sensorized devices will enhance the volume of data from various sources. Built-in immutability will ensure the integrity and security of solutions and platforms. Blockchain authentication can then enable open ecosystems without user restrictions.
Are You Looking for the Best CyberSecurity Provider?
It’s key for government contractors to achieve Cybersecurity Maturity Model Certification. Bridgehead I.T. allows companies to simplify their information technology (IT). We help increase profitability while providing a secure and stable IT infrastructure.
Our company offers enterprise-level IT services for businesses of all sizes. We’re not just a run-of-the-mill Managed Service Provider. You’ll get the full spectrum of IT service management from a business-first perspective.
Contact us today to learn about the advantages of choosing us as your CyberSecurity Service Provider.

New laws related to CMMC compliance are now in effect. Keep reading to ensure that your business is meeting all the CMMC rules.
Contact us to learn more about how Bridgehead IT can help you align your IT with your business objectives.